Alert: This source server failed to generate the changes
Description: This directory service failed to retrieve the changes requested for the following directory partition. As a result, it was unable to send change requests to the directory service at the following network address.
Event ID: 1479
Active Directory Domain Services could not update the following object in the local Active Directory Domain Services database with changes received from the following source directory service. Active Directory Domain Services does not have enough database version store to apply the changes.
User Action
Restart this directory service. If this does not solve the problem, increase the size of the database version store. If you are populating the objects with a large number of values, or the size of the values is especially large, decrease the size of future changes.
Additional Data
Error value:
8573 The database is out of version store.
Resolution:
{MS has provided the resolution in this Link}
Note: Take Backup of Registry before changing
Registry Location:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters
You need to add the Registry value “EDB max ver pages” with 32 Bit DWord Decimal value as you need with reference below:
9600 = 152 MB
12800 = 202 MB
16000 = 252 MB
19200 = 302 MB
Reboot the Server once the changes have been done.
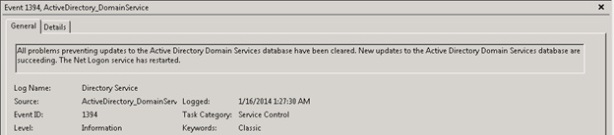
Check the Event viewer after restart; you need to get event 1394 in ADS Logs